Todays topics Computer Applications Computer Security Upcoming - PowerPoint PPT Presentation
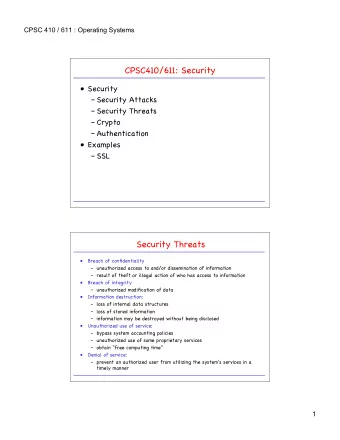
Todays topics Computer Applications Computer Security Upcoming Operating Systems ( Great Ideas, Chapter 10) Reading Great Ideas, Chapter 11 32.1 CompSci 001 Computer Security: Problem The Problem: Billions in Losses Outright theft
Today’s topics Computer Applications Computer Security Upcoming Operating Systems ( Great Ideas, Chapter 10) Reading Great Ideas, Chapter 11 32.1 CompSci 001
Computer Security: Problem � The Problem: Billions in Losses � Outright theft � Online scams � Viruses / Worms o Actual damage o Actions to avoid damage � Denial of Service � Etc. � Possible Traps (Public Systems ! ! ! ) � Trojan Horse � Onlooker � Cameras 32.2 CompSci 001
Computer Security: Defenses � Passwords � Using Secure Passwords � Keeping them Secure � Encryption � Simple � Strong � Good Practices � Like all fields, doing something stupid … � Tradeoffs � Is the cure worse than the disease? � Long Live Common Sense! 32.3 CompSci 001
Good Passwords and Cracking Briefcase (style) Combination Locks � � Brute force methods: Try all combinations Number of wheels 1. Number of position per wheel 2. Time per trial 3. How long does it take? 4. Contrast to BRUTE brute force method (Always Consider!) � Password on a computer � � + More possibilities per “wheel” � + More “wheels” (often up to user) � - Computer based cracking faster! � - Dictionary attacks Picking a good UNIX password � 32.4 CompSci 001
Encryption � When passwords fail, encryption can be fallback � Also provides extra level of difficulty � Security vs. Privacy � Many levels of encryption sophistication: Go through some of them � Single Alphabetic Substitution � Caesar: L FDPH, L VDZ, L FRQTXHUHG � Magic decoder ring? � Cryptoquote � Cracking single alphabetic substitution � Character frequency � (Length of text) 32.5 CompSci 001
Encryption � Polyalphabetic Substitution � The Vignere Cypher � The Babbit Solution � Cypher Reuse ! � One Time Pads � Can be Absolutely Secure � Computers and Random Number Generators ?! � The Key Exchange Problem � Threats � Using your “secure” channel � A padlock analogy � Diffie, Hellman, and Merkle solution 32.6 CompSci 001
Public Key Encryption � Publishing the Key! � Another padlock analogy � Diffie Proposal (1975) � Rivest, Shamir, and Adleman (RSA) � Finally came up with a practical method that met the proposed specs � Widely used now � Based on factoring (not being able to factor!) � Primes and Factoring � Examples of primes � How to factor into primes � For large numbers it is very hard 32.7 CompSci 001
Public Key Encryption � Going through an RSA example � Public key: N, K Private key: G Message: M � RSA : C = (M^K)%N M = (C^G)%N � Remainder operator (modulus) % o Wrap around property o Clock or odometer analogy � Follow example in Text . . . � Breaking the Code � Factoring � Digital Signatures � Using Private Key and Public Key � Replay attack ! � Time (analogy: newspaper in hostage picture) 32.8 CompSci 001
Politics of Strong Encryption � These unbreakable* methods called Strong Encryption � *more or less � Is any method perfect? � Government tried to keep methods from getting out � Encryption classified as a munition � Export restrictions . . . � Anecdotes � PGP – Pretty Good Privacy � Zimmerman � Legal challenges � Cat out of the bag � Recent silence from government � Has the NSA cracked it? 32.9 CompSci 001
Other Attacks (buzz words) � Many leave no trace � Password Cracking � Considered earlier � IP Spoofing � Weakness in TCP/IP; modern code deals with it � Replay Attack � Saw in Digital Signature discussion � Applies in many situations � (copy of your key made at hardware store) � Man in the Middle � Typically hardware attack � Denial of Service 32.10 CompSci 001
Whom can you trust? � How to avoid Viruses and Worms Most infections occur when trying to run unknown � � Mail or other communications programs the vector � Trapdoors Free software may have its price � � Common Sense Consider alternatives � The human factor � � Gun to the head method � The Strong Encryption Trap Forget that password? � � Bye – bye (;-( 32.11 CompSci 001
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.










![with the Metasploit Framework defcon 17 Who Are We? Chris Gates <cg [@]](https://c.sambuz.com/880262/with-the-metasploit-framework-s.webp)