1
1
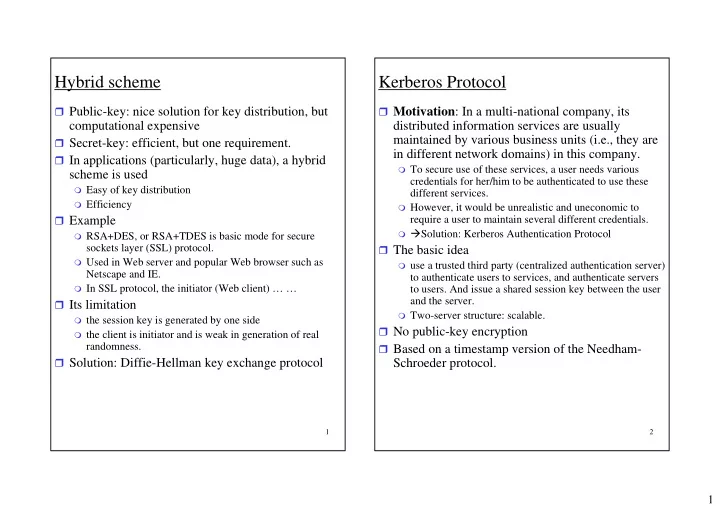
Hybrid scheme
Public-key: nice solution for key distribution, but
computational expensive
Secret-key: efficient, but one requirement. In applications (particularly, huge data), a hybrid
scheme is used
Easy of key distribution Efficiency
Example
RSA+DES, or RSA+TDES is basic mode for secure
sockets layer (SSL) protocol.
Used in Web server and popular Web browser such as
Netscape and IE.
In SSL protocol, the initiator (Web client) … …
Its limitation
the session key is generated by one side the client is initiator and is weak in generation of real
randomness. Solution: Diffie-Hellman key exchange protocol
2
Kerberos Protocol
Motivation: In a multi-national company, its
distributed information services are usually maintained by various business units (i.e., they are in different network domains) in this company.
To secure use of these services, a user needs various
credentials for her/him to be authenticated to use these different services.
However, it would be unrealistic and uneconomic to
require a user to maintain several different credentials.
Solution: Kerberos Authentication Protocol
The basic idea
use a trusted third party (centralized authentication server)
to authenticate users to services, and authenticate servers to users. And issue a shared session key between the user and the server.
Two-server structure: scalable.