SLIDE 1
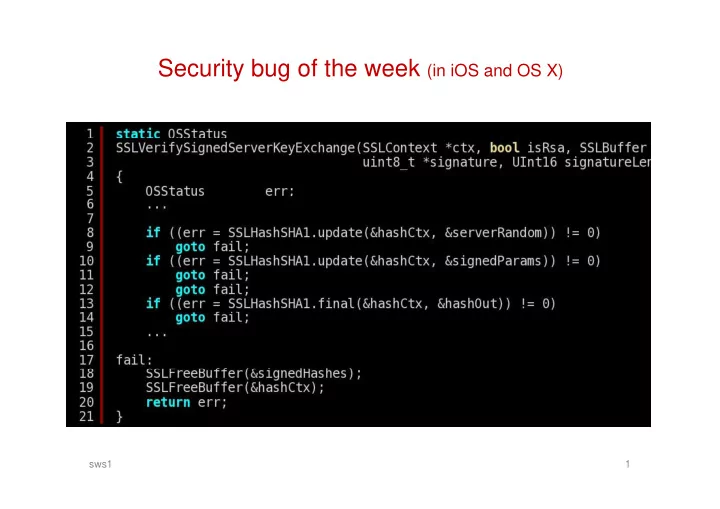
Security bug of the week (in iOS and OS X) y g
sws1 1
y g sws1 1 Attacking the stack Thanks to SysSec and Int. Secure - - PowerPoint PPT Presentation
Security bug of the week (in iOS and OS X) y g sws1 1 Attacking the stack Thanks to SysSec and Int. Secure Systems Labs at Vienna University of Technology for some of these slides sws1 2 2 Attacking the stack g We have seen how the
sws1 1
sws1 2 2
sws1 3
sws1 4
sws1 5
sws1 6
sws1 7
sws1 8
sws1 9
sws1 10
sws1 11
sws1 12
sws1 13
sws1 14
sws1 15
sws1 16
sws1 17
sws1 18
sws1 19
sws1 20
sws1 21
sws1 22
sws1 23
sws1 24
sws1 25
sws1 26
sws1 27
sws1 28
29
sws1 30
31
32
33
34
35
36
37
38
39
40
41
42
43
sws1 44
sws1 45
sws1 46
sws1 47