PHYSICAL DEVICES Introduction Lots of electronic systems - PowerPoint PPT Presentation
Dr Silvio Cesare Qualys BREAKING THE SECURITY OF PHYSICAL DEVICES Introduction Lots of electronic systems Converging with computing IT security techniques can be used Outline 1. Eavesdropping analog baby monitors 2. Disabling
Dr Silvio Cesare Qualys BREAKING THE SECURITY OF PHYSICAL DEVICES
Introduction Lots of electronic systems Converging with computing IT security techniques can be used
Outline 1. Eavesdropping analog baby monitors 2. Disabling RF-based home alarm systems 3. Hardware tampering a home alarm 4. Defeating the keyless entry of a 2000-2005 Car
Eavesdropping analog baby monitors
Analog Baby monitors? Buy new off Ebay and other places.
Using Software defined radio dongles RTL-SDR ($15) Funcube Antennas
Using upconvertors Lower frequencies not processed by SDR. Upconvert frequencies. Ham it up convertor shown:
Finding the signal using spectrum analysis High-end hardware is expensive (below left). Cheaper hw is available (RF Explorer below). 40MHz is pretty normal.
Demodulating the signal Use software spectrum analysis tools. Try AM, FM demodulation. Gqrx (Linux) HDSDR (Windows)
Mitigation Use DECT Yes.. I know DECT has been broken also.
Disabling rf-based home alarm systems
What home alarms use RF- remotes? Heaps.. Almost everything at Big-W, K-Mart, Bunnings etc
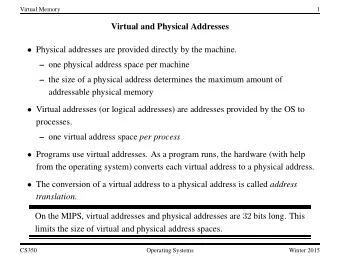
Replay attacks Real remote sends a “fixed code” to disable system. Attacker captures code and replays it with USRP etc. Works on almost all home alarms. Alarm keyfobs generally use 315 MHz and 433.92 MHz RF.
The Hardware USRP B200 right: Antennas.
Replay attacks with GNURadio Capture: Source is USRP, Sink is File. Replay: Source is File, Sink is USRP.
What is in the RF signal? Generally modulated by AM and PWM. If we demodulate the RF signal, we can see if the remote code is fixed or rolling. GNURadio and custom software.
Amplitude (am) Modulation
Pulse width modulation (pwm) Square waves generated by am demodulation.
Using cluster analysis to determine pulse widths pycluster Group similar widths together Find mean in each cluster Mean of means is the threshold.
Building a $50 arduino-based hacking box Wireless AM rx/tx pair
mitigation Use rolling codes, or challenge-response. Buy commercial alarm systems. Avoid K-Mart, Big-W et al.
Hardware tampering an alarm system
A shop at Bunnings
Interfacing with the microcontroller Disassembly reveals labelled IC (PIC) and test ports. Solder header pins. Attach PIC device programmer.
Reading secret passcodes Device programmer software. Firmware protected. Data is readable. Reveals passcode.
Potential attacks to read the firmware Glitching? Decapping the IC and changing the security fuse with UV light?
Mitigation Don’t label ICs. Assume hardware hacking. Hard to stop a well resourced attacker.
Defeating the keyless entry of a 2000-2005 Car
Building a dataset of button pushes
Phase space analysis of the rolling codes Used 10 years ago against TCP initial sequence numbers.
Predicting prng (rolling) codes Capture 3 codes from real remote. Existing software to predict PRNG. Tx with USRP.
Increasing TX range Use an amplifier.
Testing codes Capture and Replay codes. How to stop the car receiving codes? Use a Faraday cage: Aluminium Foil lined Freezer bag!
Defeating the keyless entry
Analysing the rolling code Format Preamble based on remote ID. Followed by unlock/lock/panic/trunk code. Then 16-17 bits for security in rolling code. Bits 1x1x1x1x1x1x11100x11... 3 states per bit. 1x1x1x1x1x1x11101x10... 1, 0, or a gap. 1x1x1x1x1x1x11101x00... Gaps are important. Timing 1 is twice the pulse width as a 0. An implicit gap after every 1 or 0. A gap is the width of a 0.
Analysing more The entire rolling code sequence is of a fixed time all the ones, zeros, and gaps sum to a fixed number. There are fewer x’s than 1 ’ s and 0’s. An x never follows an x.
Bruteforce? Capture 1 transmission. Use preamble of capture and then bruteforce rolling code part. Generate all numbers in range. Exclude numbers not meeting constraints. Fewer than 1 million possibilities.
Does it work? Unlocks generally in under 2 hours.
Hmm.. What’s this – a Backdoor? Some codes in bruteforce list ALWAYS unlock the car. Once known, unlocking car takes seconds not hours. Appears to be a manufacturer backdoor. TODO: How to generate from 1 capture without bruteforcing.
Mitigation Hard to mitigate without a recall. Recall is never going to happen. Install an aftermarket keyless entry or just upgrade your car. For car makers: Don’t use an algorithm to generate the rolling codes. Don’t put in backdoors.
Future work Silicon analysis Firmware recovery
Conclusion Hardware hacking is fun. Lots of real-world devices vulnerable. PRNG attacks against rolling codes have been mostly uninvestigated.
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.