Application layer: Roadmap Principles of network applications Web - PowerPoint PPT Presentation
Application Layer Application layer: Roadmap Principles of network applications Web and HTTP FTP Electronic Mail SMTP, POP3, IMAP DNS P2P applications Socket programming with UDP Socket programming with TCP 79
Application Layer Application layer: Roadmap Principles of network applications Web and HTTP FTP Electronic Mail SMTP, POP3, IMAP DNS P2P applications Socket programming with UDP Socket programming with TCP 79 CSE Department
Application Layer Pure P2P architecture no always-on server arbitrary end systems directly communicate peer-peer peers are intermittently connected and change IP addresses Topics: File distribution Searching for information 80 CSE Department
Application Layer Peer-2-Peer Architectures Unstructured Centralized: Napster Decentralized: Gnutella Hierarchical : KaZaA Structured DHT-based 81 CSE Department
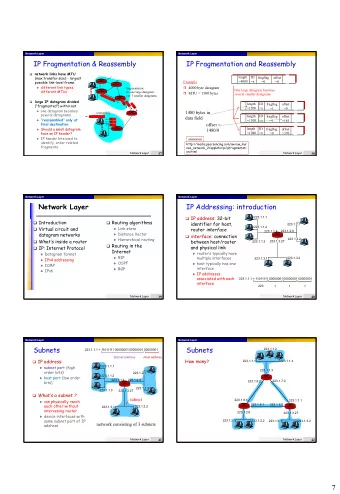
Application Layer File Distribution: Server-Client vs P2P Question : How much time to distribute file from one server to N peers ? u s : server upload bandwidth Server u i : peer i upload bandwidth u 2 u 1 d 1 d 2 u s d i : peer i download File, size F bandwidth d N Network (with abundant bandwidth) u N 82 CSE Department
Application Layer File distribution time: server-client Server server sequentially u 2 F u 1 d 1 sends N copies: d 2 u s NF/u s time Network (with d N client i takes F/d i abundant bandwidth) u N time to download Time to distribute F to N clients using = d cs = max { NF/u s , F/min(d i ) } client/server approach i increases linearly in N (for large N) 83 CSE Department
Application Layer File distribution time: P2P Server server must send one u 2 F copy: F /u s time u 1 d 1 d 2 u s client i takes F/d i time Network (with to download d N abundant bandwidth) NF bits must be u N downloaded (aggregate) fastest possible upload rate: u s + S u i d P2P = max { F/u s , F/min(d i ) , NF/(u s + S u i ) } i 84 CSE Department
Application Layer Server-client vs. P2P: example Client upload rate = u, F/u = 1 hour, u s = 10u, d min ≥ u s 3.5 P2P Minimum Distribution Time 3 Client-Server 2.5 2 1.5 1 0.5 0 0 5 10 15 20 25 30 35 N 85 CSE Department
Application Layer File distribution: BitTorrent P2P file distribution torrent: group of tracker: tracks peers peers exchanging participating in torrent chunks of a file obtain list of peers trading chunks Bram Cohen peer 86 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 87 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 88 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 89 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 90 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 91 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 92 CSE Department
Application Layer Overall Architecture Tracker Web Server C A Peer Peer [Seed] B [Leech] Downloader Peer “US” [Leech] 93 CSE Department
Application Layer BitTorrent (1) file divided into 256KB chunks . peer joining torrent: has no chunks, but will accumulate them over time registers with tracker to get list of peers, connects to subset of peers (“neighbors”) while downloading, peer uploads chunks to other peers. peers may come and go once peer has entire file, it may (selfishly) leave or (altruistically) remain 94 CSE Department
Application Layer BitTorrent (2) Sending Chunks: tit-for-tat Alice sends chunks to four Pulling Chunks neighbors currently at any given time, sending her chunks at the different peers have highest rate different subsets of re-evaluate top 4 every file chunks 10 secs periodically, a peer (Alice) asks each every 30 secs: randomly neighbor for list of select another peer, chunks that they have. starts sending chunks newly chosen peer may Alice sends requests join top 4 for her missing chunks rarest first 95 CSE Department
Application Layer Hash Table 96 CSE Department
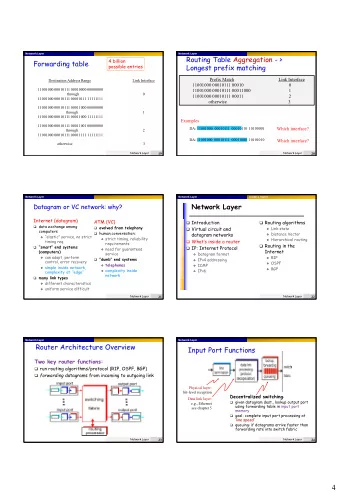
Application Layer Distributed Hash Table (DHT) DHT = distributed P2P database Database has (key, value) pairs; key: ss number; value: human name key: content type; value: IP address Peers query DB with key DB returns values that match the key Peers can also insert (key, value) 97 CSE Department
Application Layer DHT Identifiers Assign integer identifier to each peer in range [0,2 n -1]. Each identifier can be represented by n bits. Require each key to be an integer in same range. To get integer keys , hash original key. eg, key = h(“Led Zeppelin IV”) This is why they call it a distributed “hash” table 98 CSE Department
Application Layer How to assign keys to peers? Central issue: Assigning (key, value) pairs to peers. Rule: assign key to the peer that has the closest ID. Convention in lecture: closest is the immediate successor of the key. Ex: n=4; peers: 1,3,4,5,8,10,12,14; key = 13, then successor peer = 14 key = 15, then successor peer = 1 99 CSE Department
Application Layer Circular DHT (1) Overlay Link 1 Not the real link! 3 15 4 12 5 10 8 Each peer only aware of immediate successor and predecessor. “ Overlay network ” 100 CSE Department
Application Layer Circle DHT (2) O(N) messages Who’s resp 0001 on avg to resolve for key 1110 ? query, when there I am are N peers 0011 1111 1110 0100 1110 1110 1100 0101 1110 1110 Define closest 1110 as closest 1010 1000 successor 101 CSE Department
Application Layer Circular DHT with Shortcuts 1 Who’s resp for key 1110? 3 15 4 12 5 How to achieve O(log N) search time? 10 8 Each peer keeps track of IP addresses of predecessor, successor, short cuts . Reduced from 6 to 2 messages. Possible to design shortcuts so O(log N) neighbors, O(log N) messages in query 102 CSE Department
Application Layer Peer Churn 1 • To handle peer churn, require each peer to know the IP address 3 of its two successors. 15 • Each peer periodically pings its two successors to see if they 4 are still alive . 12 5 10 8 Peer 5 abruptly leaves Peer 4 detects; makes 8 its immediate successor; asks 8 who its immediate successor is; makes 8’s immediate successor its second successor. What if peer 13 wants to join? 103 CSE Department
Application Layer Chapter 2: Summary our study of network apps now complete! specific protocols: application architectures HTTP client-server FTP P2P SMTP, POP, IMAP hybrid DNS P2P: BitTorrent, Skype application service socket programming requirements: reliability, bandwidth, delay Internet transport service model connection-oriented, reliable: TCP unreliable, datagrams: UDP 127 CSE Department
Application Layer Chapter 2: Summary Most importantly: learned about protocols typical request/reply Important themes: message exchange: control vs. data msgs in-band, out-of-band client requests info or service centralized vs. server responds with decentralized data, status code stateless vs. stateful message formats: reliable vs. unreliable headers: fields giving msg transfer info about data “complexity at network data: info being edge” communicated 128 CSE Department
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.