15
Application Layer
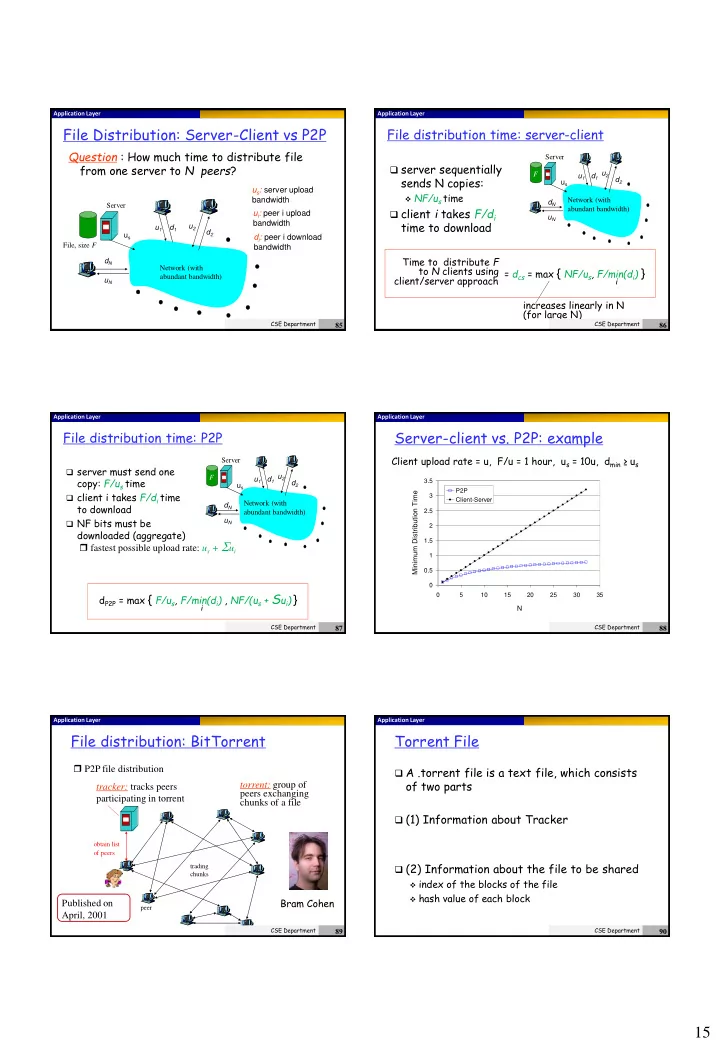
File Distribution: Server-Client vs P2P
Question : How much time to distribute file from one server to N peers?
us u2 d1 d2 u1 uN dN Server Network (with abundant bandwidth) File, size F
us: server upload bandwidth ui: peer i upload bandwidth di: peer i download bandwidth
CSE Department
85
Application Layer
File distribution time: server-client
us u2 d1 d2 u1 uN dN Server Network (with abundant bandwidth) F
server sequentially
sends N copies:
NF/us time
client i takes F/di
time to download
increases linearly in N (for large N) = dcs = max { NF/us, F/min(di) }
i
Time to distribute F to N clients using client/server approach
CSE Department
86
Application Layer
File distribution time: P2P
us u2 d1 d2 u1 uN dN Server Network (with abundant bandwidth) F
server must send one
copy: F/us time
client i takes F/di time
to download
NF bits must be
downloaded (aggregate) fastest possible upload rate: us + Sui dP2P = max { F/us, F/min(di) , NF/(us + Sui) }
i
CSE Department
87
Application Layer
Server-client vs. P2P: example
0.5 1 1.5 2 2.5 3 3.5 5 10 15 20 25 30 35
N Minimum Distribution Time
P2P Client-Server
Client upload rate = u, F/u = 1 hour, us = 10u, dmin ≥ us
CSE Department
88
Application Layer
File distribution: BitTorrent
tracker: tracks peers participating in torrent torrent: group of peers exchanging chunks of a file
- btain list
- f peers
trading chunks peer
P2P file distribution Bram Cohen Published on April, 2001
CSE Department
89
Application Layer
Torrent File
A .torrent file is a text file, which consists
- f two parts
(1) Information about Tracker (2) Information about the file to be shared
index of the blocks of the file hash value of each block
CSE Department