1 Processes and the Kernel The Kernel Processes and the Kernel - PDF document
Memory Protection Memory Protection Paging Virtual memory provides protection by: Each process (user or OS) has different virtual memory space. Machines and Virtualization Machines and Virtualization The OS maintain the page tables
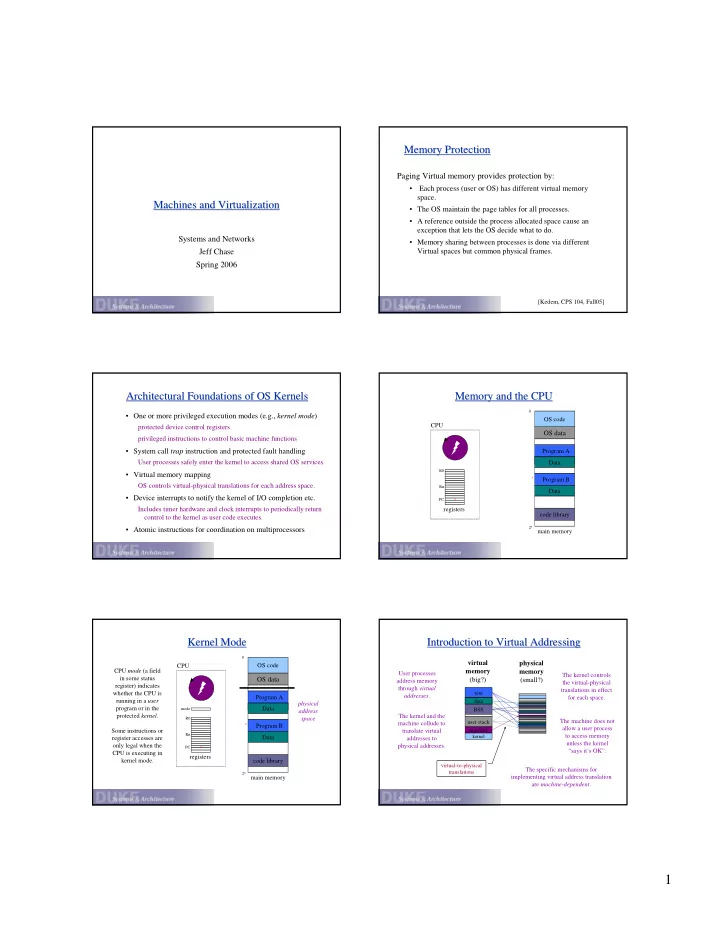
Memory Protection Memory Protection Paging Virtual memory provides protection by: • Each process (user or OS) has different virtual memory space. Machines and Virtualization Machines and Virtualization • The OS maintain the page tables for all processes. • A reference outside the process allocated space cause an exception that lets the OS decide what to do. Systems and Networks • Memory sharing between processes is done via different Jeff Chase Virtual spaces but common physical frames. Spring 2006 [Kedem, CPS 104, Fall05] Architectural Foundations of OS Kernels Memory and the CPU Architectural Foundations of OS Kernels Memory and the CPU 0 • One or more privileged execution modes (e.g., kernel mode ) OS code CPU protected device control registers OS data privileged instructions to control basic machine functions • System call trap instruction and protected fault handling Program A data User processes safely enter the kernel to access shared OS services. Data R0 • Virtual memory mapping x Program B OS controls virtual-physical translations for each address space. Rn Data • Device interrupts to notify the kernel of I/O completion etc. x PC Includes timer hardware and clock interrupts to periodically return registers code library control to the kernel as user code executes. 2 n • Atomic instructions for coordination on multiprocessors main memory Kernel Mode Kernel Mode Introduction to Virtual Addressing Introduction to Virtual Addressing 0 virtual physical CPU OS code CPU mode (a field memory memory User processes The kernel controls in some status OS data (big?) (small?) address memory the virtual-physical register) indicates through virtual translations in effect whether the CPU is text addresses . Program A for each space. running in a user data data physical data program or in the Data mode BSS address protected kernel . The kernel and the space R0 The machine does not user stack machine collude to x Program B allow a user process args/env Some instructions or translate virtual Rn to access memory Data kernel register accesses are addresses to unless the kernel only legal when the physical addresses. PC x “says it’s OK”. CPU is executing in registers kernel mode. code library virtual-to-physical The specific mechanisms for translations 2 n implementing virtual address translation main memory are machine-dependent . 1
Processes and the Kernel The Kernel Processes and the Kernel The Kernel • Today, all “real” operating systems have protected kernels. The kernel resides in a well-known file: the “machine” The kernel sets processes automatically loads it into memory ( boots ) on power-on/reset. up process in private data data execution virtual Our “kernel” is called the executive in some systems (e.g., XP). contexts to address “virtualize” the • The kernel is (mostly) a library of service procedures shared spaces machine. by all user programs, but the kernel is protected : ...and upcalls (e.g., User code cannot access internal kernel data structures directly, system call traps signals) and it can invoke the kernel only at well-defined entry points ( system calls ). Threads or shared kernel processes code and data • Kernel code is like user code, but the kernel is privileged : enter the in shared kernel for address space The kernel has direct access to all hardware functions, and services. defines the machine entry points for interrupts and exceptions . CPU and devices force entry to the kernel to handle exceptional events. Protecting Entry to the Kernel Example: System Call Traps Protecting Entry to the Kernel Example: System Call Traps Protected events and kernel mode are the architectural User code invokes kernel services by initiating system call traps. foundations of kernel-based OS (Unix, XP, etc). • Programs in C, C++, etc. invoke system calls by linking to a standard library of procedures written in assembly language. • The machine defines a small set of exceptional event types. the library defines a stub or wrapper routine for each syscall • The machine defines what conditions raise each event. stub executes a special trap instruction (e.g., chmk or callsys or int ) • The kernel installs handlers for each event at boot time. syscall arguments/results passed in registers or user stack e.g., a table in kernel memory read by the machine Alpha CPU architecture The machine transitions to kernel mode user read() in Unix libc.a library (executes in user mode): only on an exceptional event. #define SYSCALL_READ 27 # code for a read system call interrupt or trap/return exception move arg0…argn, a0…an # syscall args in registers A0..AN The kernel defines the event handlers. move SYSCALL_READ, v0 # syscall dispatch code in V0 callsys # kernel trap Therefore the kernel chooses what code move r1, _errno # errno = return status kernel will execute in kernel mode, and when. return Faults Faults The Role of Events The Role of Events Faults are similar to system calls in some respects: A CPU event is an “unnatural” change in control flow. • Faults occur as a result of a process executing an instruction. Like a procedure call, an event changes the PC. Fault handlers execute on the process kernel stack; the fault handler Also changes mode or context (current stack), or both. may block (sleep) in the kernel. Events do not change the current space! • The completed fault handler may return to the faulted context. The kernel defines a handler routine for each event type. But faults are different from syscall traps in other respects: Event handlers always execute in kernel mode. • Syscalls are deliberate, but faults are “accidents”. The specific types of events are defined by the machine. divide-by-zero, dereference invalid pointer, memory page fault Once the system is booted, every entry to the kernel occurs as a • Not every execution of the faulting instruction results in a fault. result of an event. may depend on memory state or register contents In some sense, the whole kernel is a big event handler. 2
CPU Events: Interrupts and Exceptions Mode, Space, and Context CPU Events: Interrupts and Exceptions Mode, Space, and Context At any time, the state of each processor is defined by: An interrupt is caused by an external event. device requests attention, timer expires, etc. 1. mode : given by the mode bit An exception is caused by an executing instruction. Is the CPU executing in the protected kernel or a user program? CPU requires software intervention to handle a fault or trap . 2. space : defined by V->P translations currently in effect control flow What address space is the CPU running in? Once the system is unplanned deliberate exception.cc booted, it always runs in some virtual address space. sync fault syscall trap async interrupt AST 3. context : given by register state and execution stream AST: A synchronous S ystem T rap Is the CPU executing a thread/process, or an interrupt handler? Also called a software interrupt or an event handler (e.g., Asynchronous or Deferred Procedure Call Where is the stack? ISR : I nterrupt S ervice (APC or DPC) R outine) These are important because the mode/space/context Note : different “cultures” may use some of these terms (e.g., trap, fault, exception, event, interrupt) slightly differently . determines the meaning and validity of key operations. The Virtual Address Space Process and Kernel Address Spaces The Virtual Address Space Process and Kernel Address Spaces 0 0x0 A typical process VAS space includes: text data data 0x0 • user regions in the lower half 0 BSS sbrk() V->P mappings specific to each process n-bit virtual data data 32-bit virtual jsr user stack address address accessible to user or kernel code space args/env space • kernel regions in upper half 2 n-1 shared by all processes, but accessible only to 0x7FFFFFFF 2 n-1 -1 kernel code kernel text • NT (XP?) on x86 subdivides kernel region into an and kernel data unpaged half and a (mostly) paged upper half at 2 n-1 0x80000000 0xC0000000 for page tables and I/O cache. • Win95/98 uses the lower half of system space as a 2 n -1 0xffffffff system-wide shared region. 2 n -1 0xFFFFFFFF A VAS for a private address space system (e.g., Unix, NT/XP) executing on a typical 32-bit system (e.g., x86). The OS Directs the MMU The OS Directs the MMU Virtual Address Translation Virtual Address Translation 29 virtual address 0 13 The OS controls the operation of the MMU to select: Example : typical 32-bit 00 VPN offset architecture with 8KB pages. (1) the subset of possible virtual addresses that are valid for each process (the process virtual address space ); Virtual address translation maps a (2) the physical translations for those virtual addresses; virtual page number (VPN) to a physical page frame number (PFN): (3) the modes of permissible access to those virtual addresses; address the rest is easy. read/write/execute translation Deliver exception to (4) the specific set of translations in effect at any instant. OS if translation is not need rapid context switch from one address space to another valid and accessible in requested mode. MMU completes a reference only if the OS “says it’s OK”. MMU raises an exception if the reference is “not OK”. physical address { + PFN offset 3
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.