1
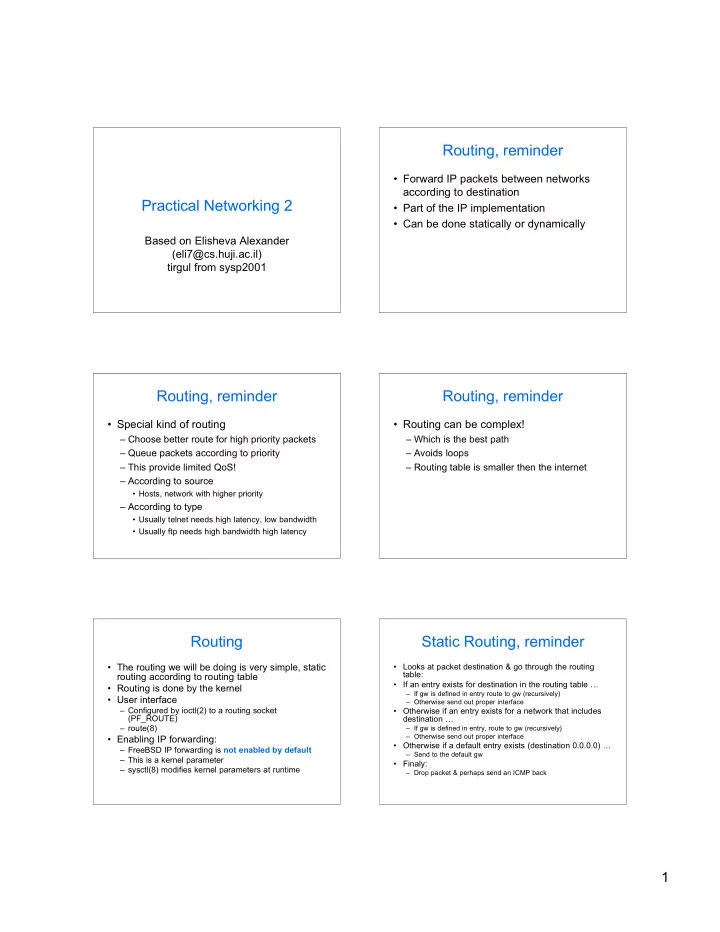
Practical Networking 2
Based on Elisheva Alexander (eli7@cs.huji.ac.il) tirgul from sysp2001
Routing, reminder
- Forward IP packets between networks
according to destination
- Part of the IP implementation
- Can be done statically or dynamically
Routing, reminder
- Special kind of routing
– Choose better route for high priority packets – Queue packets according to priority – This provide limited QoS! – According to source
- Hosts, network with higher priority
– According to type
- Usually telnet needs high latency, low bandwidth
- Usually ftp needs high bandwidth high latency
Routing, reminder
- Routing can be complex!
– Which is the best path – Avoids loops – Routing table is smaller then the internet
Routing
- The routing we will be doing is very simple, static
routing according to routing table
- Routing is done by the kernel
- User interface
– Configured by ioctl(2) to a routing socket (PF_ROUTE) – route(8)
- Enabling IP forwarding:
– FreeBSD IP forwarding is not enabled by default – This is a kernel parameter – sysctl(8) modifies kernel parameters at runtime
Static Routing, reminder
- Looks at packet destination & go through the routing
table:
- If an entry exists for destination in the routing table …
– If gw is defined in entry route to gw (recursively) – Otherwise send out proper interface
- Otherwise if an entry exists for a network that includes
destination …
– If gw is defined in entry, route to gw (recursively) – Otherwise send out proper interface
- Otherwise if a default entry exists (destination 0.0.0.0) …
– Send to the default gw
- Finaly:
– Drop packet & perhaps send an ICMP back