SLIDE 1
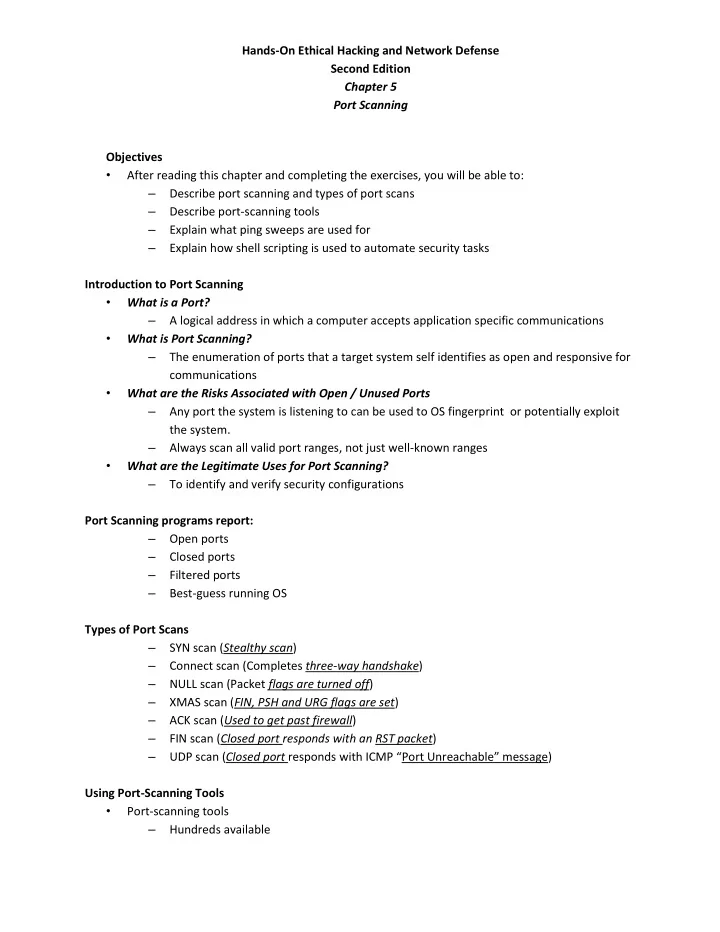
Hands-On Ethical Hacking and Network Defense Second Edition Chapter 5 Port Scanning Objectives
- After reading this chapter and completing the exercises, you will be able to:
– Describe port scanning and types of port scans – Describe port-scanning tools – Explain what ping sweeps are used for – Explain how shell scripting is used to automate security tasks Introduction to Port Scanning
- What is a Port?
– A logical address in which a computer accepts application specific communications
- What is Port Scanning?
– The enumeration of ports that a target system self identifies as open and responsive for communications
- What are the Risks Associated with Open / Unused Ports
– Any port the system is listening to can be used to OS fingerprint or potentially exploit the system. – Always scan all valid port ranges, not just well-known ranges
- What are the Legitimate Uses for Port Scanning?
– To identify and verify security configurations Port Scanning programs report: – Open ports – Closed ports – Filtered ports – Best-guess running OS Types of Port Scans – SYN scan (Stealthy scan) – Connect scan (Completes three-way handshake) – NULL scan (Packet flags are turned off) – XMAS scan (FIN, PSH and URG flags are set) – ACK scan (Used to get past firewall) – FIN scan (Closed port responds with an RST packet) – UDP scan (Closed port responds with ICMP “Port Unreachable” message) Using Port-Scanning Tools
- Port-scanning tools