Buffer Overflows with Content 2 A Process Stack Buffer Overflow - PDF document
1 Buffer Overflows with Content 2 A Process Stack Buffer Overflow Common Techniques employed in buffer overflow exploits to create backdoors Execution of additional network services via the INETD daemon The addition of new users
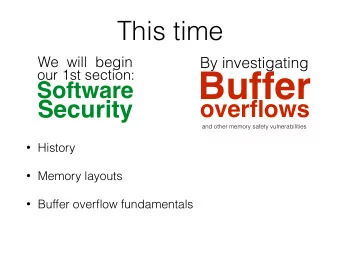
1 Buffer Overflows with Content
2 A Process Stack
Buffer Overflow • Common Techniques employed in buffer overflow exploits to create backdoors – Execution of additional network services via the INETD daemon – The addition of new users to a system – Establishing a “trust” relationship between the victim machine and the attacker’s machine 3
Example - AMD Buffer Overflow Port 2222 is a rootshell left by the AMD exploit 4
Detecting Buffer Overflows by Protocol Signatures • Protocol Signature – Look for anomalous traffic, such as remote traffic targeted at facilities that should not be accessible to a remote user. • e.g. a remote user trying to connect to the Portmapper process • Payload Signature – No-OP instructions to pad the exploit code – Script signatures – Abnormal user data and responses 5
6 IMAP Buffer Overflow
7 IMAP Buffer Overflow – Con’t
8 IMAP Buffer Overflow – Con’t
IMAP Buffer Overflow – Con’t • ls –a echo “+ + ”> /.rhosts 9
NO-OP Hex Code Based on Processor Type 10
11 Script Signatures – NO-OP Overflow
12 Script Signatures – NO-OP Overflow Con’t
Script Signatures – NO-OP Overflow Con’t • This frame shows a large number of hex 90s followed by some machine code, some ASCII strings, and a literal command /bin/sh -c 13
Abnormal Responses FTP Authentication Buffer Overflow – FTPD exploit The password supplied in response to the FTPD prompt is 14 suspiciously large
Defending Against Buffer Overflows • strcpy and strncpy • Introduce bounds checking into C programs • Stack-based buffer overflow - CPU executes code that is resident on the stack – Only code in the code space can be executed 15
16 Fragmentation
Fragmentation • Attackers can use fragmentation to mask their probes and exploits • Fragment offset is specified as a quantity of 8- byte chunk – The size of all legal nonterminal fragments must be multiples of 8 bytes • Any fragmented packets with a byte size divisible by 8, except for the last one 17
Boink Attack •IP stack has no concept of negative math •Availability DoS 18
19 Teardrop Attack
20 evilPing ….
21 evilPing
22 Modified Ping of Death
23 Modified Ping of Death
CGI Scan •The attacker is running a script that attempts a number of Web server exploits, such as /cgi- bin/rwwwshell.pl 24
25 CGI Scan – Con’t
CVE-1999-0067 26 PHF Attack
Some Example CGI CVE Entries • CVE-1999-0068 – CGI PHP mylog script allows an attacker to read any file on the target server. • CVE-1999-0467 – The Webcom CGI Guestbook programs wguest.exe and rguest.exe allow a remote attacker to read arbitrary files using the "template" parameter • CVE-1999-0509 – Perl, sh, csh, or other shell interpreters are installed in the cgi-bin directory on a WWW site, which allows remote attackers to execute arbitrary commands. 27
SGI IRIX Object Server • Scan one to goodguy-a.com yields nothing • CVE-2000-0245 • A vulnerability in an SGI IRIX object server daemon – Allow remote attackers to create user accounts – Port 5135: the SGI object server 28
SGI Object Server – Con’t • The scan to goodguy-b.com is a bust 29
SGI Object Server – Con’t • The start of the bad guy • The user zippy is added 30
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.